In this article, we are going to explore places where you can keep your cryptocurrencies and the safest ways to do so.
Online wallet
Online wallet is the easiest and least secure option. There is a plenty of types of online wallets; this role is also played by various online exchanges or online platforms such as (coinbase) or some other exchanges.
However, when you do your trades you put your trust in third-party servers. Because you don’t have any private key all that you can do is trust a third party to ensure the safety of your coins. The question is not whether the exchange or online wallet will be hacked, the question is when this is going to happen. I know some cases from my neighborhood. Therefore, I recommend that you keep in your wallets small amounts of coins only those that you need for instant transactions.
Software wallet
Software wallet is a bit safer alternative that can be installed on your computer. You can choose a full-fledged software version such as Bitcoin Core, which downloads the entire blockchain i.e. all transactions. It takes plenty of space and requires periodical synchronization, which again takes a lot of your valuable time. Much more comfortable and efficient way is the light version such as Electrum, that does not download the entire blockchain, but only the relevant transactions so the synchronization takes only tens of seconds to a few minutes.
What is important is to set a safe password and backup your wallet and private key in a safe place, ideally to make a hardcopy and to create so-called paper wallet. Using software wallets will not ensure that your coins are fully secured, either. If your computer is infected such as with keylogger (which records activities execute via your keyboard) a third party may find an easier way to access your password.
Mobile wallet
A middle-of-the-road option is to use your handset where you can download the wallet as an application. A private key is stored in an encrypted form and in case of loss you can restore the wallet and/or private key on a different device. This can be done thanks to SEED (12-24 randomly generated English words) that you should write down in a safe place, ideally on a piece of paper.
The advantage of mobile wallets is that you have them with you all the time and that they do not need to download the entire blockchain with all transactions made. When deciding on a type of mobile applications you must first know which cryptocurrencies you plan to trade and which operating system you have, iOS or Android. The same wallet may work differently on two different operating systems. For example, with Mycelium used on Android devices, you see amounts converted into your preferred currency while iOS displays the amount in dollars and euro only.
Three mobile wallets from which you will surely choose:
Mycelium is one of the simplest and hence most popular ways to keep your bitcoins safe. With one seed you can create multiple accounts and import your wallet from a paper wallet. When sending BTC you can choose the size (and also the time) of the transaction fee. Mycelium is compatible with plenty of exchanges or hardware wallets (see below) and supports blockchain-based fiat accounts. So, you can connect Mycelium with a credit card.
Unlike Mycelium, Coinomi enables storing of dozens of various cryptocurrencies under a single seed. The wallet converts the entire portfolio into USD in real time and, owing to ShapeShift, you can exchange various altcoins one for another at the current exchange rate in the application’s interface. You can set the size of the transaction fee and you are a holder of a private key. Another advantage of this wallet is its anonymity. The transactions are not tracked and your IP address is encrypted. A downside is that it cannot be used on a iSO device. However, this version is already underway.
Copay is a wallet for more discriminating users. It makes it possible to create multiple wallets with a private key that you have under control. It even supports multisig wallets, that you can share with up to six users. Thanks to this feature, Copay offers the possibility of verifying the transaction by other people i.e. it offers mutual control to those who keep the cryptocurrency as part of a company or an organization. You can couple the application with a hardware wallet, display amounts in USD and choose the size of the transaction fee. You can also connect Copay to Coinbase to quickly and safely buy or sell bitcoin.
Of the dozens of mobile wallets available in the market, each has some pro and con. When choosing a wallet, try out more types. I am sure you will find one meeting your expectations. Lots of bitcoin wallets have their light versions such as for Litecoin, Ethereum etc. so if you hold various coins you will most likely need more than just one application. Don’t forget that wallets can be used for keeping smaller amounts for instant use. Hodling large amounts of coins is a job for a different device.
Hardware wallet
The safest way to avoid hacking is to move your private key from online to offline. Hardware wallet is a device that helps your private key be safely kept for several types of cryptos (see below). With a small stick similar to your flash disc connected to your PC the actual confirmation of your private key will be done outside the PC protecting you from malware such as a keylogger. Below you can see a few hardware wallets to choose from:
Trezor

When connected to your PC, Trezor will download Trezor Bridge to be used for communication with the online wallet MyTrezor. Like in traditional wallets, it is used for sending and receiving cryptos. Log in to Trezor via your PIN displayed on Trezor’s screen in a 3×3 table. Using a “blind keyboard”, hover the cursor of your mouse over the table and fill it out. This method represents outstanding protection against hackers denied to watch you work with your keyboard.
Trezor supports Windows 7-10, OS 10.13 + and Linux. Using seed, you will create the backup (you can choose more English words than standard 12 words). These words enable you to restore your private key on a new Trezor in case of loss, theft or destruction of the old one. Also, you can strengthen your protection by adding passphrase encryption, a password without which the seed would not work.
Trezor supports the following cryptocurrencies (as of January 2018): Bitcoin, Litecoin , DASH, Zcash, Bitcoin Cash / Bcash (BCH), Bitcoin Gold (BTG), Ethereum (ETH), Ethereum Classic (ETC), ERC-20 Tokens, Expanse (EXP), UBIQ (UBQ), NEM (XEM), Namecoin and Dogecoin.
Ledger Nano S
Coming from France, Leger Nano S is, among all hardware wallets, the main competitor to Trezor. It bears reminiscence of a traditional flash disc. Ledger was the first hardware wallet to support Ethereum. Nano S is the third version released in 2016, with an embedded display that allows you to use it, like Trezor, on your computer infected with keylogger.
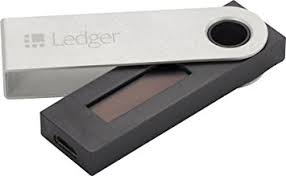
You can make a backup of the ledger by using 24 English words (that you must write down after your first login). The ledger is delivered in a package protected with a tape. Therefore, if you find out that the tape is damaged you’d better send it back; it’s the indication of someone having tampered with the device.
Ledger supports the following types of alternative currencies (as of January 2018): Bitcoin (BTC), Bitcoin Cash (BCH), Bitcoin Gold (BTG), Ethereum (ETH), Ethereum Classic (ETC), Litecoin (LTC), Dogecoin (DOGE), Zcash (ZEC), Ripple (XRP), Dash (DASH), Stratis (STRAT), Komodo (KMD), Ark (ARK), Expanse (EXP), Ubiq (UBQ), Vertcoin (VTC), Viacoin (VIA), Neo (NEO), Stealthcoin (XST), Stellar (XLM), Hcash (HSR), Digibyte (DGB), Qtum (QTUM) and PivX (PIVX).
Duel: Trezor vs. Ledger?!
Compared with Trezor Ledger has a disadvantage in not supporting passphrase encryption. On the other hand, it’s cheaper by around USD 20 (depending on e-shop). As to the dimensions, it is more compact but more user-friendly with a more elaborated virtual wallet. Also, the storing capacity is bigger.
Bottom line:
As said before, dealing with cryptos means always a risk. Safety first is the rule you should be aware of all times. If you decide to put your trust in a third party you should repeat that the question is not whether an exchange or online wallet will be hacked, the question is when this is going to happen The same rule (of keeping small amounts of coins needed for instant transactions) at exchanges or online platforms applies to hardware wallets.
If you decide to “hodl” a large number of coins, buy a hardware wallet. No matter which brand you choose – Trezor, Ledger or any other “cold storage” such as KeepKey or Bitlox – hodl your crypto offline out of the reach of hackers.